At this year’s annual hacking conference, Black Hat Asia, a team of security researchers revealed how cybercriminals are sneakily using stolen credit cards and the “Someone else will get it” option. the Apple Online Store in a scheme that saw more than $400,000 stolen in just two years. .
9to5Mac Security Bite brought to you exclusively by Mosyle, the only unified Apple platform. Making Apple devices work-ready and enterprise-secure is everything we do. Our unique integrated approach to management and security combines industry-leading Apple-specific security solutions for fully automated hardening and compliance, next-generation EDR, AI-powered Zero Trust, and proprietary privilege management with the most powerful and modern Apple MDM. on the market. The result is a fully automated unified Apple platform, currently used by more than 45,000 organizations to make millions of Apple devices ready to work effortlessly and affordably. Request your EXTENDED TRIAL today and understand why Mosyle is all you need to work with Apple.

According to Gyuyeon Kim and Hyunho Cho of South Korea’s Financial Security Institute, in September 2022, she and her colleague discovered a series of cyberattacks against more than 50 legitimate online stores, revealing significant data breaches. However, upon further analysis, they discovered that malicious actors were interested in much more than a quick theft of user data.
Cybercriminals have successfully manipulated the payment pages of these online stores to transmit credit card and personal information to their servers, in addition to legitimate servers, in order to remain undetected.
“These threat groups used various evasion strategies to prevent their phishing pages from being detected by site administrators and users, using multiple vulnerabilities and tools,” the security duo said in their Black Hat briefing.
However, stealing credit cards was only part of the plan.
According to the study, one of the main ways bad actors profited was by taking advantage of the Apple Online Store’s “opt-out contact” policy. “The ultimate goal of this operation was financial gain,” Kim explained.
The program begins by selling new Apple products at “discounted” prices at online second-hand stores in South Korea. From what the research describes, these appear to be the equivalent of a Craiglist or eBay. When the buyer reaches an agreement with the seller, or in this case, the malicious actors, the previously stolen credit card details are used to purchase the product itself from the Apple Store.
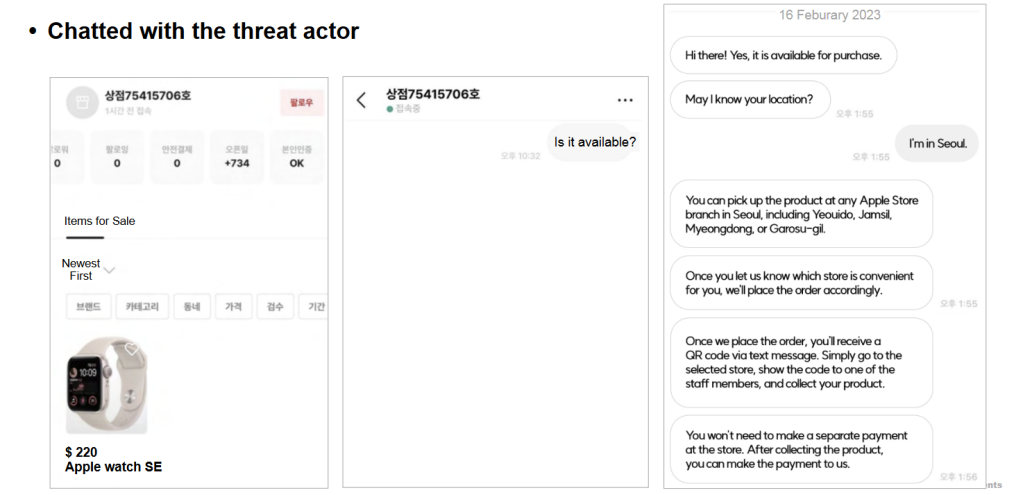
Image via Black Hat Asia/Gyuyeon Kim and Hyunho Cho
Instead of having it shipped, the cybercriminals set the item to the “Someone else will pick it up” option on Apple’s website. This allows authorized individuals to pick up online orders at an Apple store by presenting a government photo ID and QR code/order number. The second-hand store shopper would be designated as the third party able to recover the product unknowingly purchased with a stolen credit card.
Only after the buyer collects the product does he pay, probably through the thrift store. The bad actor could miss out if the buyer doesn’t send the agreed amount.
For example, a brand new iPhone 15 worth $800 could be listed for $700 on the second-hand market. The price would be low enough to generate interest but high enough not to appear like a scam. After finding an interested buyer, the criminals would purchase the device using a stolen credit card number obtained through their phishing operations and pocket the $700 the buyer paid at the thrift store.
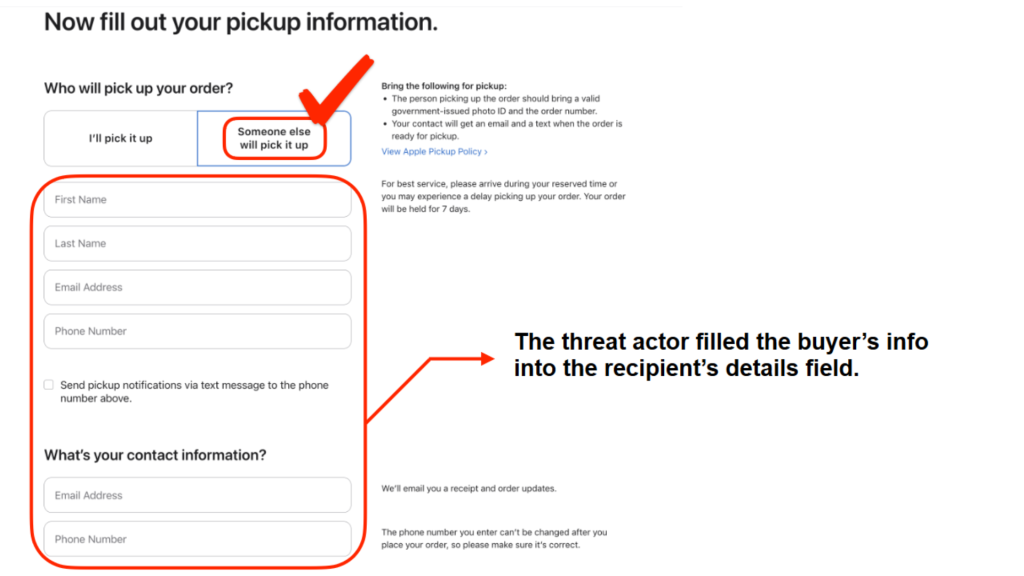
Image via Black Hat Asia/Gyuyeon Kim and Hyunho Cho
“A stolen card was used to make a $10,000 payment at an Apple Store, but Apple’s refusal to cooperate due to internal regulations hampered the investigation,” citing the researcher’s presentation at Black Hat Asia in a more extreme case. “Despite Mr. Yoon’s efforts to immediately report the incident to the card company and the police, Apple’s lack of cooperation resulted in delays of more than a month in the investigation. Apple’s refusal to provide any information, citing internal policy, has drawn criticism both domestically and in the United States, despite the company’s emphasis on privacy.
Gyuyeon Kim and Hyunho Cho call this project “PoisonedApple,” which they say has generated $400,000 over the past two years. The current perimeter extends to South Korea and Japan, but there is no reason for criminals in other countries, including the United States, to start doing the same.
Who is behind this scheme?
Researchers believe the culprits are based somewhere in China because the phishing web pages are registered through a Chinese ISP. Miraculously, while browsing Dark Web forums, they also found simplified Chinese mentions of the same email address in the source code.
Check out the full Black Hat briefing and presentation here.
More in this series
Follow Arin: Twitter/XLinkedIn, Discussions
FTC: We use automatic, revenue-generating affiliate links. More.