Microsoft released Sysmon 12, and it comes with a useful feature that saves and captures all data added to the Windows Clipboard.
This feature can help system administrators and incident responders track the activities of malicious actors who have compromised a system.
Those who are not familiar with Sysmon, also known as System Monitor, this is a Sysinternals tool that monitors Windows systems for malicious activity and logs them to the Windows Event Log.
Sysmon 12 adds clipboard capture
With the release of Sysmon 12, users can now configure the utility to generate an event whenever data is copied to the Clipboard. Clipboard data is also saved in files that are only accessible to an administrator for later review.
Since most attackers will use the Clipboard when copying and pasting long commands, monitoring data stored on the Clipboard can provide useful information on how an attack was carried out.
To get started, download Sysmon 12 from its dedicated Sysinternal page or https://live.sysinternals.com/sysmon.exe.
Once downloaded, run it from an elevated command prompt, as it needs administrative privileges to run.
Simply running Sysmon.exe without any arguments will bring up a help screen, and for more information you can go to the Sysmon page of Sysinternals.
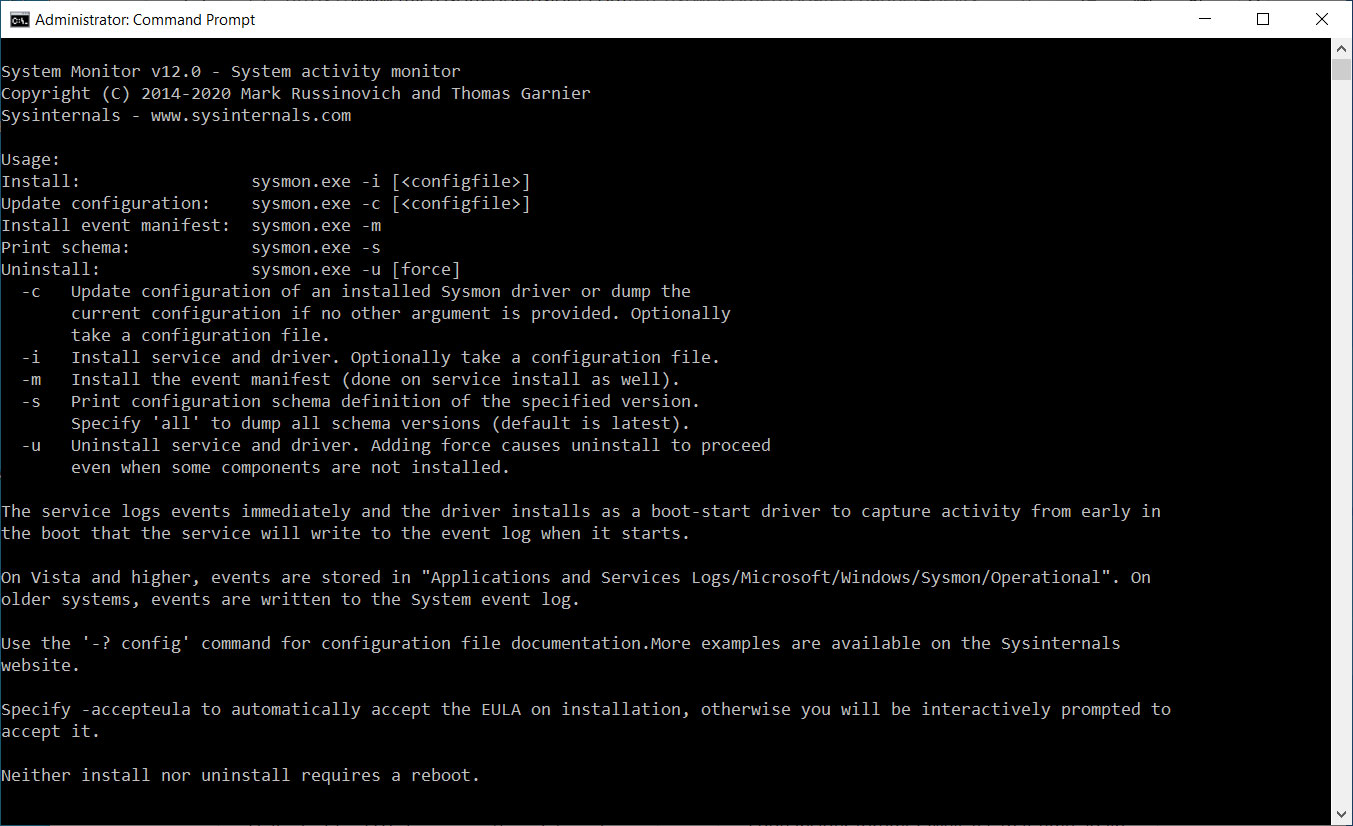
Without any configuration, Sysmon will monitor basic events such as process creation and file time changes.
It is possible to configure it to record many other types of information by creating a Sysmon configuration file, which we will do to enable the new ‘CaptureClipboard’ directive.
For a very basic configuration that will allow logging and clipboard capture, you can use the configuration file below:
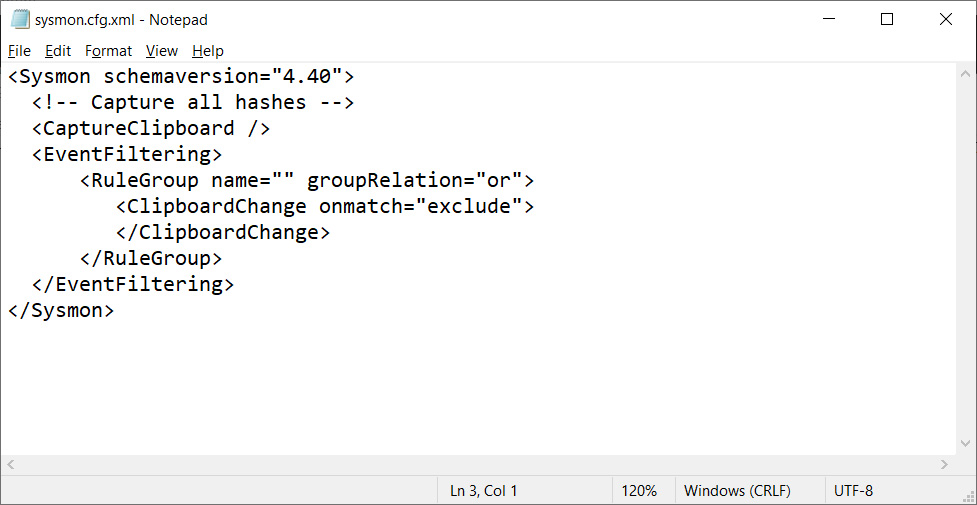
To start Sysmon and instruct it to use the above configuration file, you must enter the following command from an elevated command prompt:
sysmon -i sysmon.cfg.xmlOnce started, Sysmon will install its driver and start collecting data quietly in the background.
All Sysmon events will be logged in ‘Applications and Services Logs / Microsoft / Windows / Sysmon / Operational‘in the Event Viewer.
When the CaptureClipboard feature is enabled, when the data is copied to the Clipboard, it generates an “Event 24 – Clipboard Changed” entry in the Event Viewer, as shown below.
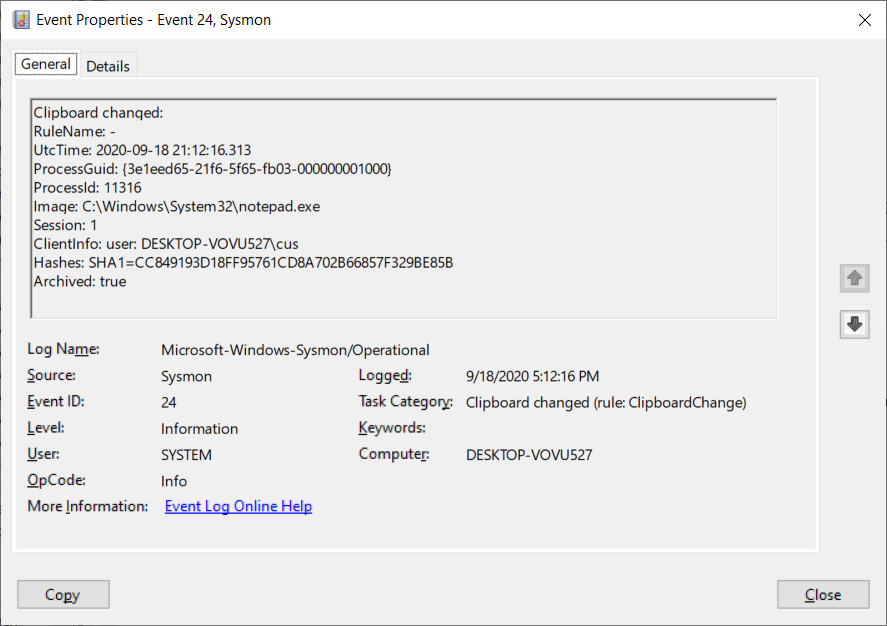
The event log entry will show which process stored the data to the clipboard, the user who copied it and when it was done. However, it will not show the actual data that was copied.
The copied data is instead saved to the protected C: Sysmon C: Sysmon folder in files named clip-SHA1_HASH, where the hash is provided in the above event.
For example, the event displayed above would have the contents of the Clipboard stored in the C: Sysmon CLIP-CC849193D18FF95761CD8A702B66857F329BE85B file.
This C: Sysmon folder is protected by a system ACL, and to access it you need to download the psexec.exe program and launch a cmd prompt with system privileges using the following command:
psexec -sid cmdAfter launching the new system command prompt, you can navigate to the C: Sysmon folder to access the saved clipboard data.
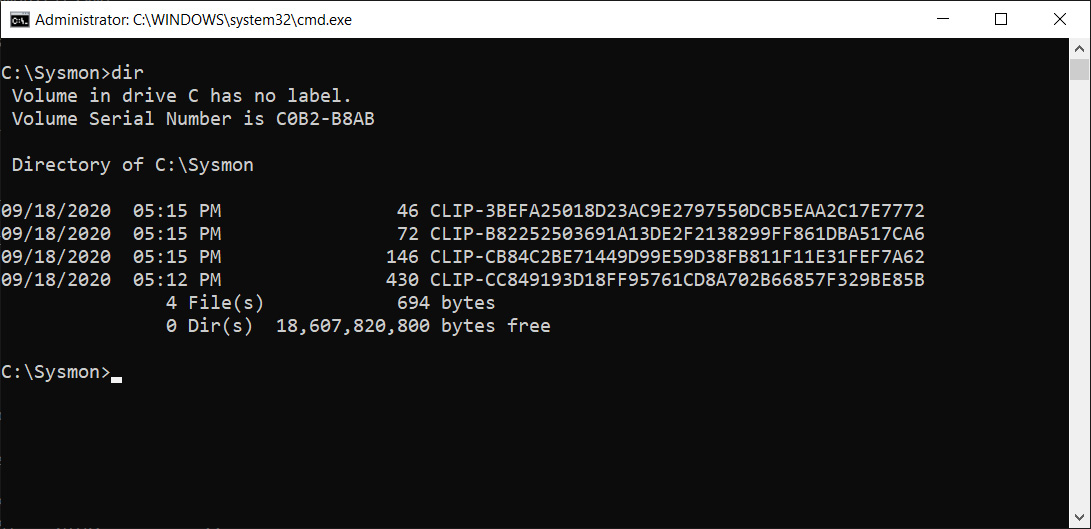
When opening the CLIP-CC849193D18FF95761CD8A702B66857F329BE85B file, you can see that it contains a PowerShell command that I copied to the clipboard from Notepad.exe.
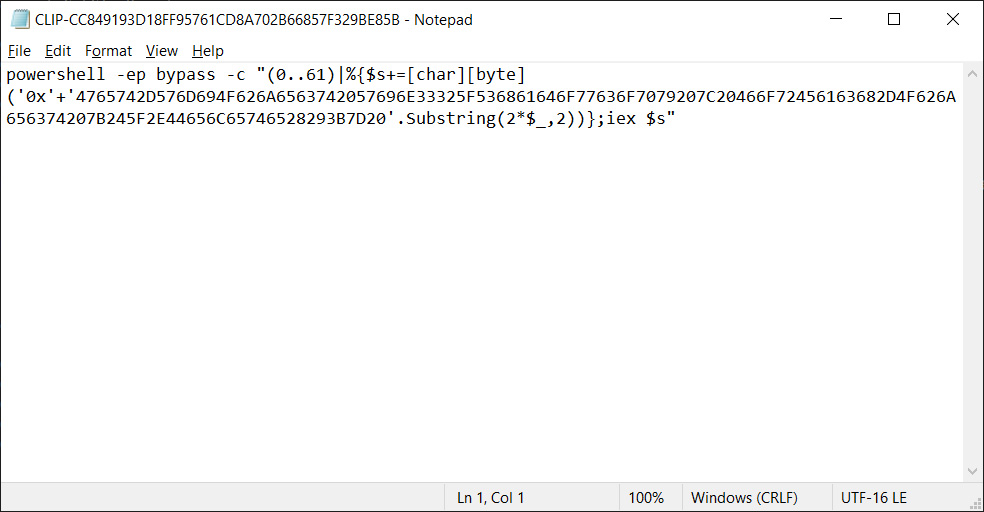
This PowerShell command is used to wipe out volume shadow copies in Windows, which can be used by an attacker who wants to make it harder to restore deleted data.
Having this information shows how useful this feature can be when responding to incidents.
Another useful feature added in Sysmon 11 will automatically create backups of deleted files, allowing administrators to recover files used during an attack.
Learn more about Sysmon
For those who want to learn more about Sysmon, it is highly recommended that you read the documentation on the Sysinternals site and play with the tool.
There is no better way to learn how to use this program than by creating configuration files and seeing what events are written to the event log.
More information about the different directives used in Sysmon can be obtained by entering the command sysmon.exe -s all.
If you want to use a predefined Sysmon configuration file designed to monitor malicious traffic and threats, you can use SwiftOnSecurity’s Sysmon configuration file on GitHub.
















