Security researchers have come up with a way to block the recently disclosed PetitPotam attack vector that allows hackers to easily take control of a Windows domain controller.
Last month, security researcher GILLES Lionel unveiled a new method called PetitPotam that forces a Windows machine, including a Windows domain controller, to authenticate against a malicious actor’s NTLM relay server using Microsoft Encrypting File System Remote Protocol (EFSRPC).
The actors of the threat would then relay this authentication request to the Active Directory certificate services of a targeted domain via HTTP., Where the attacker would receive a ticket for granting a Kerberos ticket (TGT), allowing him to assume the role of identity of the domain controller.
After the vector was disclosed, researchers quickly began testing the method and illustrated how easy it was to dump credentials and take over a Windows domain.
Using this attack, a malicious actor can take full control of a Windows domain, including issuing new group policies, new scripts, and deploying malware to all devices, such as ransomware.
Last week, Microsoft published an advisory titled “Mitigating NTLM Relay Attacks on Active Directory Certificate Services (AD CS)” that explains how to mitigate NTLM relay attacks.
To prevent NTLM relay attacks on networks where NTLM is enabled, domain administrators should ensure that services that enable NTLM authentication use protections such as Extended Protection for Authentication (EPA) or signing features such as SMB signing, ”the Microsoft review explained.
“PetitPotam takes advantage of servers that do not have Active Directory Certificate Services (AD CS) configured with protections against NTLM relay attacks. The mitigations described in KB5005413 * tell customers how to protect their AD CS servers from such attacks.
Although Microsoft’s suggestions may prevent NTLM relay attacks, they provide no indication of blocking PetitPotam, which can be used as a vector for other attacks.
“It can also be used for different attacks, such as NTLMv1 downgrade and relay machine account on computers where that machine account is a local administrator,” Lionel told BleepingComputer when he disclosed the vector to attack for the first time.
Microsoft’s response to recent vulnerabilities, such as PetitPotam, SeriousSAM, and PrintNightmare, has been of great concern to security researchers who believe Microsoft is not doing enough to protect its customers.
I would like to clarify my position on #Microsoft in general
A lot has improved over the past 10 years .. a lot .. especially with Windows 10/2016.
Today, many fellow security researchers whom I respect a lot are working there.I criticize Microsoft’s response to recent ones.
– Florian Roth (@ cyb3rops) August 1, 2021
Block PetitPotam attacks using NETSH filters
The good news is that researchers have found a way to block the PetitPotam unauthenticated remote attack vector using NETSH filters without affecting local EFS functionality.
NETSH is a Windows command line utility that allows administrators to configure network interfaces, add filters, and change Windows Firewall configuration.
This weekend, Craig kirby shared a NETSH RPC filter that blocks remote access to the MS-EFSRPC API, effectively blocking the unauthenticated PetitPotam attack vector.
According to a security researcher Benjamin Delpy, you can use this filter by copying the following content to a file called ‘block_efsr.txt’ and saving it to your desktop.
rpc
filter
add rule layer=um actiontype=block
add condition field=if_uuid matchtype=equal data=c681d488-d850-11d0-8c52-00c04fd90f7e
add filter
add rule layer=um actiontype=block
add condition field=if_uuid matchtype=equal data=df1941c5-fe89-4e79-bf10-463657acf44d
add filter
quitNow open an elevated command prompt and type the following command to import the filter using NETSH.
netsh -f %userprofile%desktopblock_efsr.txtYou can verify that the filters have been added by running the following command:
netsh rpc filter show filterAfter running the command, netsh should display two filters, one for c681d488-d850-11d0-8c52-00c04fd90f7e and another for df1941c5-fe89-4e79-bf10-463657acf44d, as shown below.
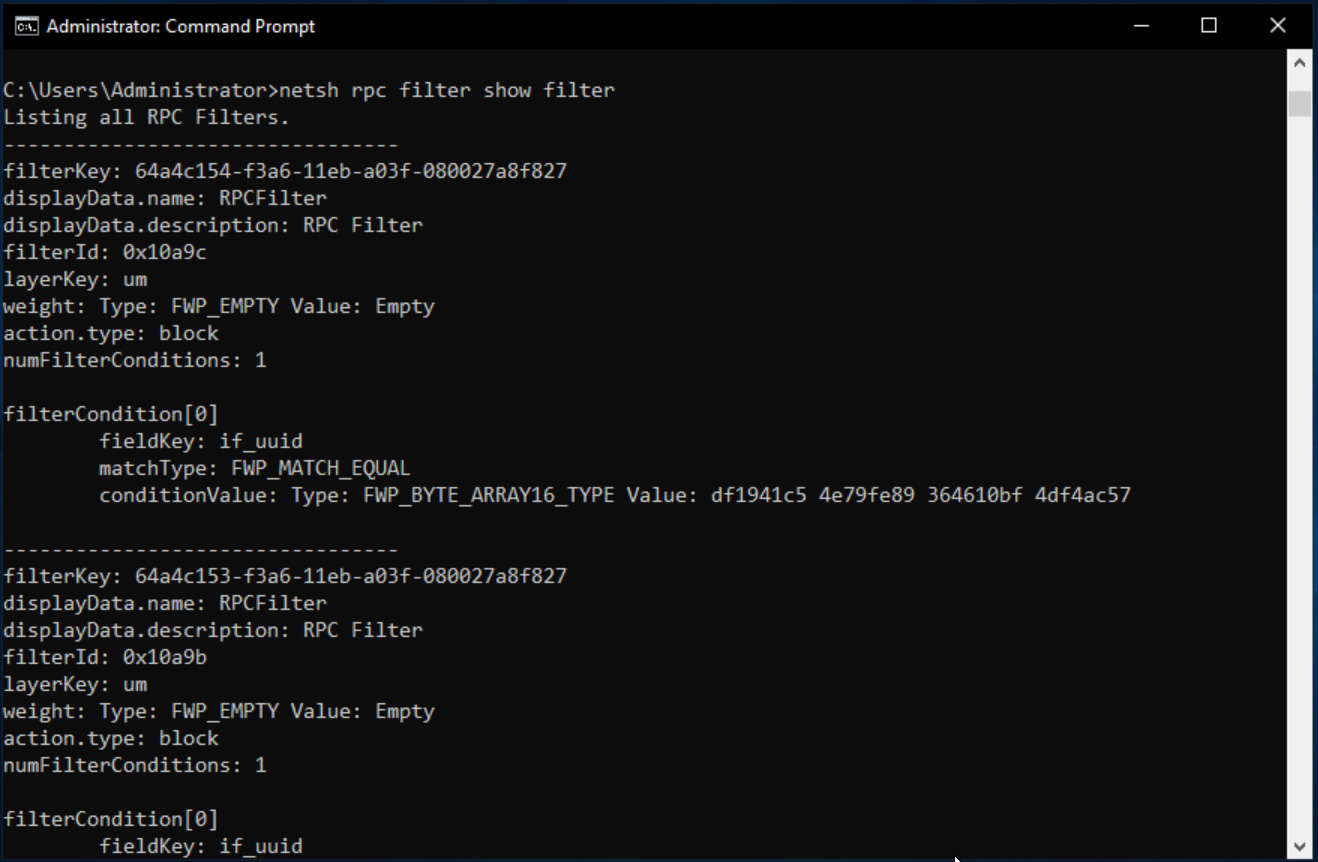
With these filters in place, the PetitPotam vector will no longer work, but EFS will continue to work normally on the device.
If Microsoft fixes the API to prevent this vector, you can remove the filters using the following command:
netsh rpc filter delete filter filterkey=[key]The filter key can be found when viewing the list of filters configured as described above.