Google is cracking down on companies that violate its privacy and ad fraud rules. cheetah … [+]
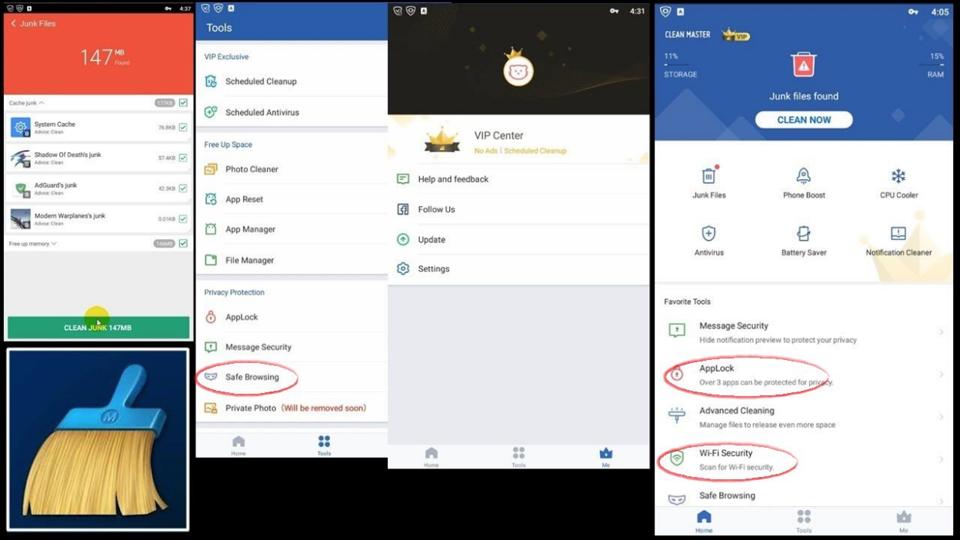
In February, Google removed 600 apps from its Play Store. Among them was an app called Clean Master, a security tool promising antivirus protection and private browsing. It had more than a billion installations before its expulsion and, despite Google’s ban, is one of the most downloaded Android apps of all time and is probably still running on millions of phones. .
Although Google did not comment on what it knew about the app, created by Cheetah Mobile in China, Forbes learned that a security company has provided evidence to the tech giant that the tool collects all kinds of private data for web use.
This includes websites that users have visited from the application’s “private” browser, their search engine queries and the names of their Wi-Fi hotspots, up to more detailed information such as how they scrolled through the web pages they visited, according to the security company researcher. , who also provided the information Forbes.
Cheetah, a state-owned company that sees Chinese tech giant Tencent as a major investor, says it needs to monitor users to protect them and provide them with useful services.
But the research, conducted by Gabi Cirlig, a researcher at the cybersecurity company White Ops, comes after previous allegations of potential privacy issues with Cheetah’s apps. In 2018, Google fired its CM File Manager app from its app store for violating its advertising fraud policies. (At the time, in response to a report by Buzzfeed News, Cheetah denied having the opportunity to wrongly claim clicks on the ads for profit, as has been alleged). Last year, VPNpro warned of potentially “dangerous” permissions required by devices, such as the ability to install apps.
Cheetah Mobile’s Clean Master was one of the most popular Android apps ever. But it was … [+]
According to Cirlig, it’s not just Clean Master that monitors user activity on the web. According to Cirlig, three other Cheetah products – CM Browser, CM Launcher and Security Master – have done the same with hundreds of millions of downloads. He surveyed apps last year to find out about the behavior before sharing his research with Forbes. He discovered that Cheetah collects information from devices, encrypts the data and sends it to a web server – ksmobile[.]com. Through reverse engineering of this encryption process, he was able to determine what data was being collected from users’ phones.
“Technically speaking, they have a privacy policy that covers everything and gives them a blank check to exfiltrate everything,” says Cirlig. “I can’t know for sure what they are infringing on. It’s just that they’re playing ball in a gray area and it’s up to researchers like us to stand up and call fault whenever they think that they cross the line. I personally think they cross the line. “
Reply from Cheetah
Cheetah says it East collects web traffic from users and other data, but does so primarily for security reasons. For example, it monitors Internet browsing to ensure that the sites that users visit are not harmful. It also helps provide certain services, such as suggesting recent research on trends.
As for accessing names on Wi-Fi networks, Cheetah said Forbes the reasoning was pretty much the same: to prevent users from joining malicious Wi-Fi networks. “We do not collect data and we have no plans to track user privacy,” said a spokesperson.
The company says it complies with all local privacy laws, does not sell users’ private data, and does not return information to a Chinese server, but to an Amazon Web Services system outside the country . Cirlig, however, noted that the domain where the information was relayed was registered in China. And Cheetah himself is based in Beijing.
“No good reason to collect data”
Two independent security researchers and Cirlig say there are much safer ways to collect information. For websites and Wi-Fi hotspots, they could turn information into “hashes” – pieces of random letters and numbers that represent websites. Machines can read them and compare these hashes to previously reported hash databases of malicious websites or Wi-Fi networks without humans having to view them. (Cheetah says hashes would complicate his security checks, as he has to look for subtle changes in Wi-Fi names, such as when a zero is changed to “o” or previously unknown malicious sites.)
Will Strafach, founder of the Guardian iOS security app and researcher on smartphone privacy issues, said there was “no good reason for [Cheetah] to collect this information. “
Graham Cluley, a security analyst who has spent much of his career working for antivirus companies, said such data collection was “clearly a concern”. There are ways for a security company to check for threats without having to collect as much information, which could potentially be used to reduce user privacy. “
“Even if the applications themselves request permissions, I hope a security product will explain why it needs certain data and try to justify its roaring data,” added Cluley.
What is the potential for abuse?
Referring to the breadth of information collected by Cheetah, it would be possible to anonymize a user by browsing their web browsing habits, Wi-Fi hotspots and phone identification numbers, said Cirlig .
“The problem is that they correlate user behavior – what applications their audience uses, what sites they browse, etc. – with specific data that can be very easily linked to a real person behind this phone. . . . So even if you want to prevent any kind of tracking, it’s not enough to just change your phone, but the entire infrastructure you use.
“Even if for some reason they wipe out all personal data on the server side, the incredibly huge installation base still allows them to leverage their depersonalized data in the style of Cambridge Analytica.”
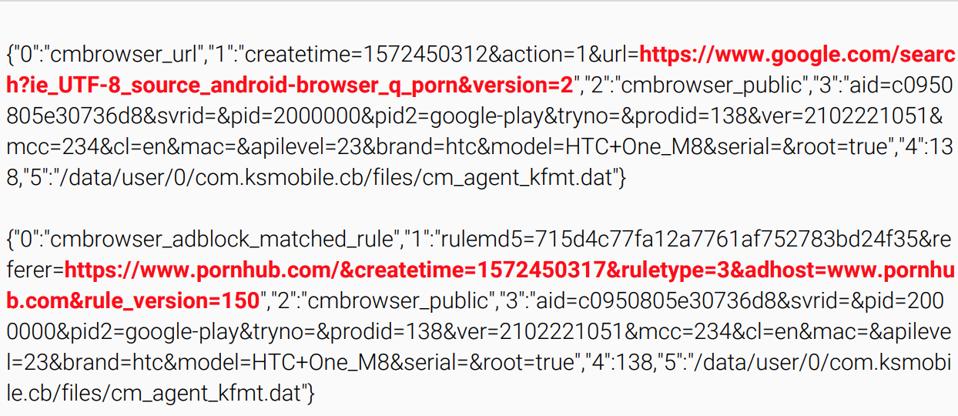
Cheetah Mobile Google search tracking logs via its CM Browser. Cheetah says he must … [+]
White Ops said it informed Google of the behavior in December. In February, Cheetah discovered that its Google Play Store, AdMob and AdManager accounts had been suspended. Google did not respond ForbesQuestions about whether the White Ops’ warnings led to Cheetah’s ban.
Cheetah, which has been listed on the New York Stock Exchange since May 2014, is appealing Google’s decision and claims to be working with the tech giant to address its concerns. If he can’t find a way to get back to Google Play, the ban will seriously lower his earnings. In the first nine months of 2019, almost a quarter of Cheetah Mobile’s revenue came from services hosted by Google.



















