Mobile threat campaign tracked as wandering mantis has been linked to a new wave of compromises directed at French mobile phone users, months after expanding its targeting to include European countries.
As many as 70,000 Android devices are believed to have been infected as part of the active malware operation, Sekoia said in a report released last week.
Attack chains involving Roaming Mantis, a financially motivated Chinese threat actor, have been known to deploy a piece of banking Trojan named MoqHao (aka XLoader) or redirect iPhone users to malware collection landing pages. credentials that mimic the iCloud login page.

“MoqHao (aka Wroba, XLoader for Android) is an Android Remote Access Trojan (RAT) with information-stealing and backdoor capabilities that likely spreads via SMS,” Sekoia researchers said. .
It all starts with a phishing SMS, a technique known as smishing, tricking users with parcel delivery-themed messages that contain malicious links, which, when clicked, proceed to download the malicious APK file, but only after determining if the victim’s location is within French borders.
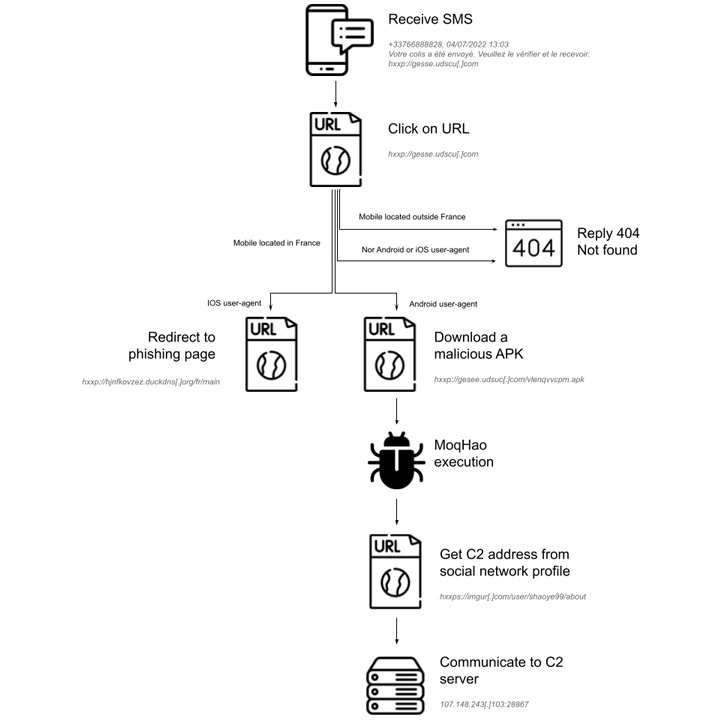
If a recipient is outside France and the device’s operating system is neither Android nor iOS – a factor verified by checking the IP address and User-Agent string – the server is designed to respond with a “404 Not found” status code.

“The smishing campaign is therefore geo-fenced and aims to install Android malware, or collect Apple iCloud IDs,” the researchers point out.
MoqHao typically uses domains generated through the Duck DNS dynamic DNS service for its first stage delivery infrastructure. Additionally, the malicious app impersonates the Chrome web browser app to trick users into granting it invasive permissions.
The spyware trojan provides a window of opportunity for remote interaction with infected devices, allowing the adversary to stealthily harvest sensitive data such as iCloud data, contact lists, call history , SMS messages, among others.
Sekoia also assessed that the data amassed could be used to facilitate extortion schemes or even sold to other threat actors for profit. “more than 90,000 unique IP addresses that requested the C2 server distributing MoqHao,” the researchers noted.