Microsoft has discovered new malware used by the Nobelium hacking group to deploy additional payloads and steal sensitive information from Active Directory Federation Services (AD FS) servers.
Nobelium, the threat actor behind last year’s SolarWinds supply chain attack that led to the compromise of several US federal agencies, is the hacking division of the Russian Foreign Intelligence Service (SVR) , commonly known as APT29, The Dukes or Cozy Bear.
In April, the US government formally accused the SVR division of carrying out “the large-scale cyber espionage campaign.”
Cybersecurity firm Volexity has also linked attacks to APT29 operators based on tactics seen in previous incidents dating back to 2018.
Used in nature since April 2021
The malware, dubbed by researchers at the Microsoft Threat Intelligence Center (MSTIC) Foggy web, is a “passive and highly targeted” backdoor that abuses the Security Assertion Markup Language (SAML) token.
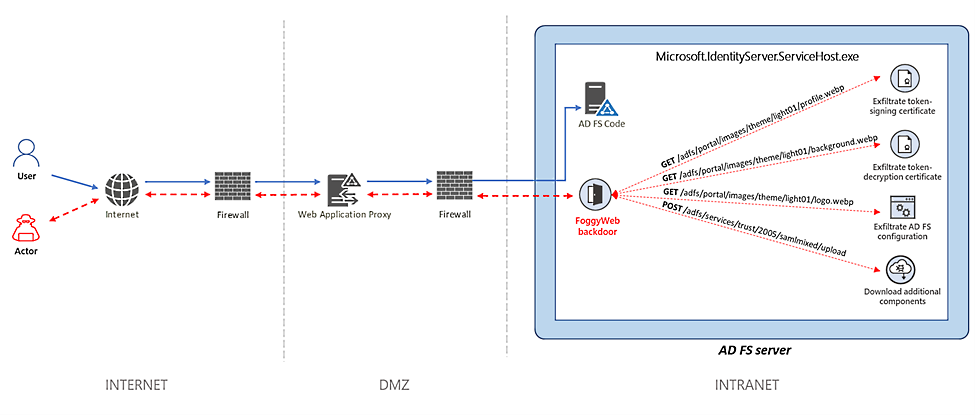
It is designed to help attackers remotely exfiltrate sensitive information from compromised AD FS servers by configuring HTTP listeners for actor-defined URIs to intercept GET / POST requests sent to the AD FS server corresponding to the templates. ‘Custom URIs.
“NOBELIUM uses FoggyWeb to remotely exfiltrate the compromised AD FS server configuration database, decrypted token signing certificate and token decryption certificate, as well as to download and run additional components,” Microsoft said.
“It can also receive additional malicious components from a command and control (C2) server and execute them on the compromised server.”
FoggyWeb works as a persistent backdoor that allows SAML token abuse and configures HTTP listeners for actor-defined URIs to intercept GET / POST requests sent to AD FS server (from Internet / intranet) that match to custom URI templates.
Russian state hackers have been observed using the FoggyWeb backdoor in the wild since April 2021.
FoggyWeb Defense Tips
Microsoft has already alerted savvy customers who have been targeted or compromised using this backdoor.
Organizations that believe they may have been breached or compromised are encouraged to:
- Audit on-premises and cloud infrastructure, including configuration, per-user and per-application settings, forwarding rules, and other changes the actor could have made to maintain access
- Remove user and application access, review the configurations for each, and reissue new, strong credentials in accordance with documented industry best practices.
- Use a hardware security module (HSM) as described in Securing AD FS Servers to Prevent FoggyWeb Exfiltration of Secrets.
In May, Microsoft researchers also revealed four other malware families used by Nobelium in their attacks: a downloader known as “BoomBox”, an HTML attachment named “EnvyScout”, a downloader, and a shellcode launcher. named ‘VaporRage’ and a charger known as’ ‘NativeZone,’
They detailed three other strains of Nobelium malware used for layered persistence in March: a command and control backdoor dubbed “GoldMax”, a persistence tool and malware dropper named “Sibot” and a HTTP tracker tool tracked as “GoldFinder”.


















